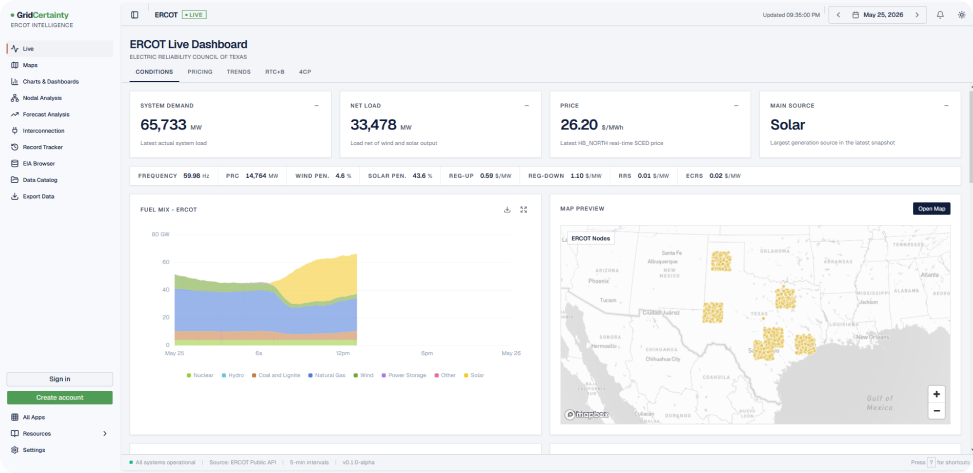
Validate Interconnection in Minutes, not Months
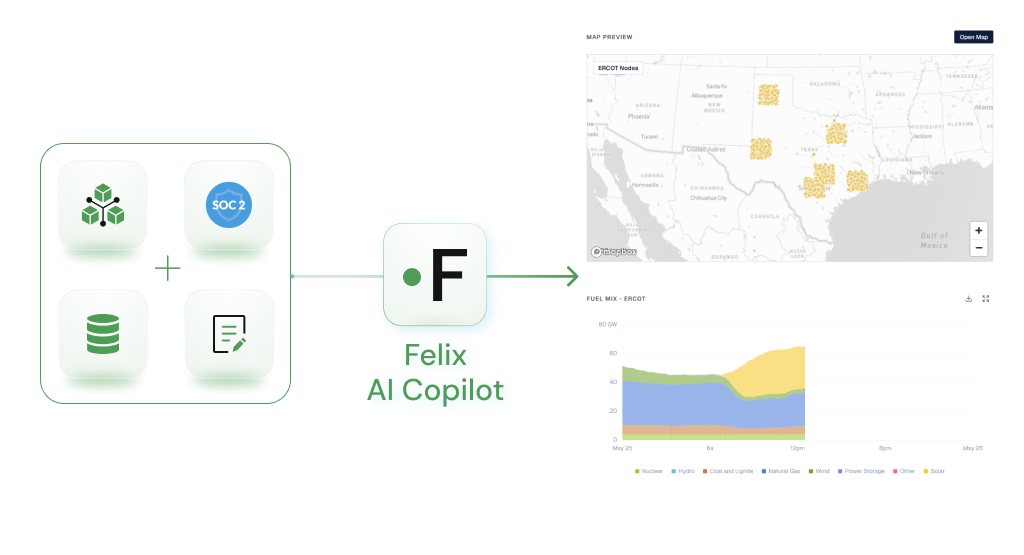
Felix helps energy infrastructure teams find viable sites, de-risk development, and get to power faster.
Proven Impact in Grid Transformation
Our ISO-accurate tools empower transmission teams to de-risk interconnection and accelerate grid transformation. With over 700 GW modeled and a 97%+ accuracy rate, Felix has uncovered $5B+ in cost discrepancies to help 100+ developers secure a faster path to power.
>$5B
100+
700+
>97%
ISO-Aligned Methodology
We replicate ERIS and NRIS studies, not FCITC approximations.
Intelligent Insights
Developed by engineers who’ve worked at ISOs, utilities, and top developers.
Proven at Scale
500+ GW modeled. $3B+ in ISO errors uncovered. 100+ developers trust us.
Products that scale clean energy projects
Felix supports generation and load developers, transmission planning engineers, utility teams, and ISOs by streamlining study processes and enabling transparent, aligned decision-making across stakeholders. Paces helps energy infrastructure teams find viable sites, de-risk development, and get to power.
Generation Developers
- Enable Generation Developers to make smarter siting and queue decisions
- Increase success rates and reduce wasted capital
- Directly accelerates projects reaching operation
Load Developers
- Enable large loads to enter the queue more efficiently and transparently
- Find build-ready sites with the fastest path to power
- Evaluate impacts of competitor projects and de-risk future buildout
Independent Power Producers
- Make confident development and interconnection decisions across your portfolio
- De-risk new projects with ISO-accurate cost and capacity certainty before you commit capital
- Compare sites, queue positions, and expansion options on one transparent platform
Development Process Designed for Visibility
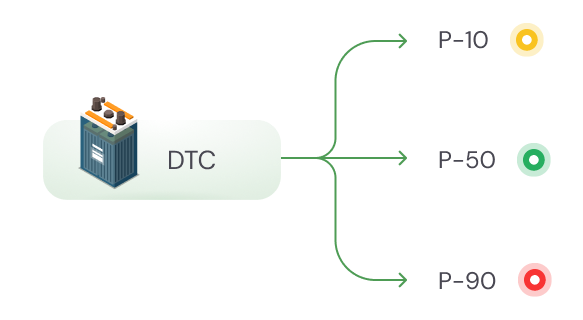
Headroom Capacity
- Enable Generation Developers to make smarter siting and queue decisions
- Increase success rates and reduce wasted capital
- Directly accelerates projects reaching operation
Local Studies Tool
- Enable Generation Developers to make smarter siting and queue decisions
- Toggle local queue assumptions across flexible, across numerous custom scenarios
- Re-runs full ISO study methodology for fast, accurate results
- Compare scenarios based on knowledge of competing projects in the queue